dentify all the strings for the following language:
Q: ase answer true or false
A: As we know During the detailed design of a new computer, the device and digital logic levels of the ...
Q: PROVIDE JS SOURCE CODE Design a web page with a text box (username) where the user can enter a name ...
A: In the starting the condition for ID is given as ID consists of 4 digits only. Where as in the end, ...
Q: Why are there so many different partitioning algorithms in use by operating systems, and why are the...
A: Given: Why are there so many different partitioning algorithms in use by operating systems, and wh...
Q: illustrate the execution of the in-place heap sort algorithm in the following input sequence: {2, 5,...
A:
Q: if Analysis using Excel I. Cox Electric makes electronic components and has estimated the followin...
A: It is defined as the basic building blocks of an electronic circuit or electronic system or electron...
Q: With practical examples, discuss the difference(s) between a Web Server software and a Web Client so...
A: Web Server Software: A web server is nothing but a combination of hardware and software that uses hy...
Q: Question 5 What would be the result of y the following line of code? y= 10 2 - 9 + 4; 15 Previous 14
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: Write a php program to take the current room temperature from the user in degree celsius and try to ...
A: Answer: Approach:- 1. Take the current room temperature (in C) from the user using the readline m...
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position...
A: The Internet of Things (IoT) is a remarkable concept: In one way it is still very theoretical and in...
Q: Explain why NoSQL databases became popular in the 2000s and compare and contrast their characteristi...
A: NoSQL databases (aka "not merely SQL") do not use relational tables to store data. NoSQL databases a...
Q: Perform the following base conversions a) 1100110110, L16 b) 1234g*
A:
Q: Problem 1. Answer the following questions. No mark will be given if no valid reason is given. (a) (1...
A:
Q: PYTHON! Solve problem by using PYTHON Program to remove the ith occurrence of the given word in list...
A: Here I have taken input from the user and then stored the input into a list. Next, I have printed th...
Q: Q.4: Explain how Files or Applications Data are converted into bits in OSI Model, also mention the i...
A: Ans 4) part a) Methodology of how files data are converted into bits in OSI model,please refer below...
Q: The big endian and little endian are two different types of people. Also, look up the history of thi...
A: Endianness is a term that can be in order that the counting as sequence order as the bytes that can ...
Q: By using jakob Nielsen usability attributes, evaluates a system/interface/equipment ?
A: Lets discuss the solution in the next steps
Q: void main() "Cppbuz".
A: let us see the answer:- Hence the correct option is d i.e.6,7 I am attaching the output
Q: Question:: Describe the TM that accepts the language, L= {w e{a,b,c}* | w contains equal number of a...
A: Given: L = {w belongs to {a,b,c}* | w contains equal number of a's b's and c's} Logic to build Turin...
Q: How to systematically improve a Linux computer's security.
A: Answer- First of all the Linux systems are secure as compared to another operating systems. Now if y...
Q: Assume the following rules of associativity and precedence for expressions: Precedence Higbert 1, no...
A: The order of evaluation will depend on the number of operand needed to perform operation and so we m...
Q: What do you mean by subnet mask?
A: According to the question the subnet cover are by and large utilized for 32 pieces manage used to se...
Q: How are the words "receive" and "returns" used in the suggested procedure?
A: How are the words "receive" and "returns" used in the suggested procedure
Q: What do you mean by subnet mask?
A: According to the question the subnet cover are by and large utilized for 32 pieces manage used to se...
Q: te a Java program to find the sum of digits of a user entered number in O(1) time comple
A: Lets see the solution.
Q: Many firms now employ cloud computing as part of their information infrastructure. quickly discuss c...
A: Introduction: Cloud computing refers to the on-demand availability of computer system resources, par...
Q: Write a Java program to find the sum of digits of a user entered number till that number becomes one...
A: Coded using Java.
Q: How to systematically improve a Linux computer's security.
A: Solution :: There are lots of Linux servers out there - (good or well enough) many that it's impos...
Q: Stanford Enterprises has provided its manufacturing estimated and actual data for the year end. The ...
A: Solution ::
Q: Question:: Describe the TM that accepts the language, L= {w e{a,b,c}* | w contains equal number of a...
A: Answer :-
Q: What is the difference between equals() and == in Java?
A: What is the difference between equals() and == in Java?
Q: Log-based recovery and the shadow-copy scheme have different overheads when data are added to new di...
A: answer is
Q: Solve problem by using PYTHON Program to remove the ith occurrence of the given word in list where w...
A: Introduction:
Q: What do you mean by subnet mask?
A: According to the question the subnet cover are by and large utilized for 32 pieces manage used to se...
Q: Using the list of threats to InfoSec that were shown in this chapter, find and describe three exampl...
A: There are several types of information security risks, including software assaults, intellectual pro...
Q: Computer Science You are part of an IT team who is known as a first responder to a data breach. Plea...
A: 1) First I will call IT data security professionals 2) I will restore files from backup and change a...
Q: = ax2 + bx + c. • Ask the user for the coefficients a, b and c of a quadratic function f (x) Output ...
A: Hi, as per the given question, we are given a Python problem along with the code and sample output. ...
Q: Briefly state how you think blockchain technology and cryptocurrency might affect the economy in the...
A: Briefly state how you think blockchain technology and cryptocurrency might affect the economy in the...
Q: ɪᴏɴ, ᴀɴᴅ ᴛ ɪꜱ ᴛʜᴇ ᴛɪᴍᴇ. ᴛʜᴇ ɪɴɪᴛɪᴀʟ ᴠᴇʟᴏᴄɪᴛʏ ᴀɴᴅ ᴀᴄᴄᴇʟᴇʀᴀᴛɪᴏɴ ᴏꜰ ᴛʜᴇ ᴏʙᴊᴇᴄᴛ ɪꜱ 1.5 ᴍ/ꜱ ᴀɴᴅ 2 ᴍ/ꜱ2, ʀ...
A: Assembly language: Assembly language is a low level programming language. It tells the computer dire...
Q: Briefly state how you think blockchain technology and cryptocurrency might affect the economy in the...
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful. Tha...
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array :...
A: Solution: Given, 1- fill the array with integers >20 2- print the content of the array 3- find ...
Q: :the output of (Print "a", "b", "c") is abc O ab c O abc O O
A: According to the question this double quotes in print function help to print the string with the spa...
Q: If Moore's Law is to hold, Rock's Law must fal
A: Find the answer with reason given as below:
Q: There are blank 3 digit counting numbers that are made using only the odd digits 1,3,5,7,9?
A: Odd numbers are whole numbers that cannot be divided exactly into pairs.
Q: Because you might want to use a symbolic constant instead of an integer literal in your code.
A: Introduction: People who read the source code of a computer program might not understand an integer ...
Q: Show that there exists a simple 3-polytope that has that J23 fos = 1 and fo: = 0 for i > 9. 3, J24 2...
A:
Q: A processor's primary structural components should be mentioned and briefly characterised.
A: A computer device is made up of various components which help in its effective functioning and proce...
Q: :the output of (Print "a", "b", "c") is abc O ab c abc O C
A: answer is
Q: In simple words, descript the following security aspects: Authentication, Integrity, Confidentiality...
A: Confidentiality:- Confidentiality is synonymous with privacy. Measures made to ensure confidentialit...
Q: Write a program that accepts two four-digit binary numbers, converts them to decimal values, adds th...
A: ANSWER: we can convert binary to decimal in java using Integer.parseInt() and a custom method getDec...
Q: structure and get the following information from three users: Name (String), Employee ID (String) an...
A: Lets see the solution.
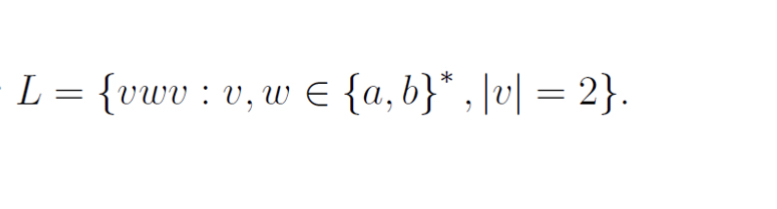
![L = {vwv : v, w E {a,b}* , \v] = 2}.](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F8f6ac4d0-b737-4535-a31c-dac4d1c0727f%2F0641e6c4-b77b-4b04-a932-ca6d8ae78e4a%2Ffvpy65s_processed.jpeg&w=3840&q=75)
Step by step
Solved in 2 steps with 1 images

- Given the following definitions: U={a,b,c, d, e, f, g} A={a, c, e, g} B={a,b,c,d} find A n BTrue or False. (A—B)(A+B) = A^2 —B^2Write a function that displays an n-by-n matrix using the following header: void printMatrix(int n)Each element is 0 or 1, which is generated randomly. Write a test program that prompts the user to enter n and displays an n-by-n matrix.
- In c programming without pointer and function Problem Statement A matrix is a 2D array of numbers arranged in rows and columns. We give you a Matrix of N rows and M columns. Now your task is to do this operation on this matrix: If the value matches with the current row and column number then add 3 with the value. If the value matches with only the current row number then add 2 with the value. If the value matches with only the current column number then add 1 with the value. Input Format The first line contains N is the number of rows in this matrix and M is the number of columns in this matrix The second line contains a 2D array Arr[i][j]. Constraints 1 <= N, M <= 10 0 <= Arr[i][j] <= 100 Output Format Print the matrix after the operation is done. Sample Input 0 3 31 1 11 1 11 1 1 Sample Output 0 4 3 3 2 1 1 2 1 1Q_8. Decription:- Given an array of integers, write a PHP function to find the maximum element in the array. PHP Function Signature: phpCopy code function findMaxElement($arr) { // Your code here } Example: Input: [10, 4, 56, 32, 7] Output: 56 You can now implement the findMaxElement function to solve this problems. .6s^2 while s=1.5
- 10. Let A = {c, n, b}, B = {x, y} and C = {0, 1}. Find a) АХВХС b) СХВХА c) BXCXCa C++ program that creates a two-dimensional integer array (4x3) initialized with user given data. The program should have the following functions: • Print the sum of all values in the array. • Print the average of all the values in the array. • Take row number from user and print the sum of the values in that specified row.(use loop and no if statement) • Take column number from user and print the sum of the values in that specified column.(use loop and no if statement)in c language Use one-dimensional arrays to solve the following problem. Read in two sets of numbers, each having 10 numbers. After reading all values, display the unique elements common to both sets of numbers. Use the smallest possible array to solve this problem.
- Write a function in C language that takes student number as a value and adds the numbers in each digit of your student number to different dynamic arrays separately My student number = 1910213570 Example student number 25698574 Result = 7 5 9 5 4 8 6 2Write a function in C programming that takes a two-dimensional 20x20 integer array as a parameter. The function must return the index of the row on which the sum of the elements is the minimum.Match the C-function on the left to the Intel assemble function on the right. W: cmpl $4 movl %edi , %edi jmp .L4(,%rdi,8) %edi .L3: movl $17, %eax ret .15: movl $3, %eax int A ( int x , int y) { int a ; if ( x == 0 ) else i f ( x == 1 ) a = 3 ; else i f ( x == 2 ) a = 2 0 ; else i f ( x == 3 ) a = 2 ; else i f ( x == 4 ) a = 1 ; ret .L6: a = 17; movl $20, %eax ret .L7: movl $2, %eax ret else a = 0; .L8: return a ; movl $1, %eax .L2: ret . section .rodata . L4: .quad .L3 .quad .L5 .quad .L6 .quad .L7 .quad .L8 X: testl %edi, %edi je cmpl je cmpl je стр1 je cmpl .L16 $1, %edi .L17 $2, %edi .L18 $3, %edi int B (int x, int y) { int a; switch (x) { .L19 $4, %edi %al movzbl %al, %eax case 0: a = 17; break; sete break; case 1: a = 3; case 2: a = 20; break; case 3: a = 2; break; case 4: a = 1; a = 0; } return a; ret .L16: break; movl $17, %eax ret .L17: movl $3, %eax } ret .L18: movl $20, %eax ret .L19: movl ret $2, %eax











