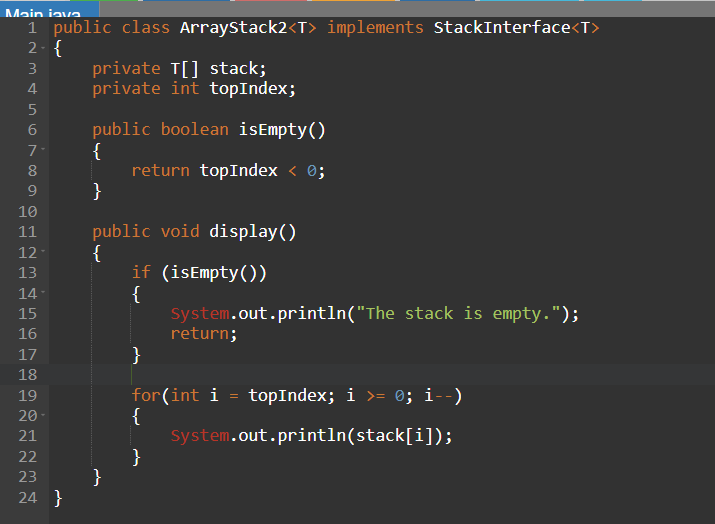
IN JAVA Implement the method public void display() which displays the entries in a stack starting from the top. If the stack is empty, print “The stack is empty”. Add the method to ArrrayStack2.java. You do not need to modify StackInterface.java
Q: Which paradigm is more challenging for compilers to implement, VLIW or superscalar? Why?
A: Introduction: During the course of a single clock cycle, a superscalar processor may issue more than…
Q: clients of the Information Systems Audit Division
A: User Information Systems' function inside the audit department: The User Information System is a…
Q: Processors that can read and act on encrypted data and system instructions have been proposed. The…
A: Introduction of computer security: Computer security is the protection of computer systems and…
Q: Give an account of what happens when a student accesses www.google.com on their laptop while it is…
A: For long-distance wireless LAN connections, a router is needed. A router connects network devices to…
Q: Consider the following system of equations: System of Equations where the constants A and B are…
A: Here's a function in MATLAB that implements the Newton-Raphson iteration for solving the system of…
Q: Which three goals must be met by a network in order for it to function properly? How long can you…
A: Introduction : A network is a group of two or more computers or other devices connected together to…
Q: The amount of usable storage space on a hard disk may be affected, however, if RAID is utilized to…
A: Please refer to the following step for the complete solution to the problem above.
Q: Determine, analyze, and contrast several implementations of the back-end compiler?
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Difference between holding the copyright and a license to use software.
A: Copyright Consideration of a person's or organization's intellectual property rights is referred to…
Q: Is it feasible to discuss the testability of the compiler?
A: Testing a hypothesis or theory requires testability. Testability includes research methodologies and…
Q: To get started, a database transaction must be initiated. We're going to focus on the bright side of…
A: Database: A database is a structured collection of data that is organized to enable efficient…
Q: Can someone please explain to me this question? ASAP??!!! 8. Consider the throughput example shown…
A: This question is asking you to consider a network with M client-server pairs and to derive a general…
Q: When it comes to the various tasks that it does, what is the central processing unit's actual…
A: Introduction CPU: The primary element of a computer's processing capacity is its Central Processing…
Q: Keep in mind the importance of wireless networks in the developing nations of the globe. The use of…
A: 1) Wireless and wired and networks are both types of computer networks that allow computers and…
Q: Specifically, why is a firewall so crucial, and what does it do? How do you recommend people utilize…
A: Please refer to the following step for the complete solution to the problem above.
Q: Accessible through cloud computing are the following, followed by an explanation of how cloud…
A: We can understand Cloud as like internet. Cloud computing is use of remote system only to support…
Q: Is there any functionality or features included within the Compiler's Phases? Is it possible to show…
A: In this question, it is asked to list the functions of all the compiler's phases. An example of…
Q: I'll give you a brief overview of the compiler if you'd like, and we can talk about the idea of…
A: Introduction: A compiler is a software that converts high-level programming language source code…
Q: It's important to detail the different storage devices on a computer system, including their…
A: Computer Systems: Computer systems are a combination of hardware and software components, working…
Q: Are there any more programs that are related to the compiler? In a few words, how would you…
A: There are several programs related to compilers, here are some of them: Interpreter: An interpreter…
Q: hat do you believe to be the most important distinctions between a traditional phone network and the…
A: Here are some of the key differences between traditional phone networks and the internet. :-
Q: It would be very useful to distinguish between integrity constraints and permission limits.
A: Introduction: Integrity constraints and permission limits are two different concepts in the context…
Q: The transport layer is responsible for facilitating the transfer of data over the Internet. It is…
A: Operating system:- A computer's operating system (OS) is a piece of software that enables the…
Q: As contrast to a traditional client-based storage solution, there are several advantages to using a…
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: Can several architectures for the compiler's backend be tried out
A: Yes, several architectures for the compiler's backend can be tried out.
Q: Think about how the internet has developed through time, and what kinds of technical architecture it…
A: Describe Internet growth. Two 1965 MIT Lincoln Lab computers interact using packet-switching.B&N…
Q: Please help me with this assignment. For this assignment you will implement divide and conquer…
A: Introduction Sorting: The act of sorting involves placing items in a predetermined order. Numerous…
Q: For a compiler to be effective and precise, it has to take into account a variety of factors, such…
A: Introduction : A compiler is a software application that takes in source code written in a…
Q: How can we keep the CPU from idling as it processes many instructions? Which steps do you think are…
A: Introduction A CPU, or Central Processing Unit, is the primary component of a computer that performs…
Q: To function properly and effectively, a network has to satisfy three conditions. Please provide a…
A: INTRODUCTION: Computers, servers, mainframes, network devices, peripherals, and other devices are…
Q: How should one go about deciding on a plan to keep a physical network safe? Three different…
A: Network security:- Network security is the activity of defending systems, programs, and networks…
Q: You may argue that its importance to corporate operations makes it a must-have. What preparations…
A: Introduction: A bug-free, high-quality software may boost a company's image. Therefore, company…
Q: Let's have a look at the testability recommendations and the compiler summary.
A: Introduction: The ability to put a hypothesis or theory to the test via the means of an experiment…
Q: When someone says they're using "parallel processing," what exactly do they mean
A: Management abilities in clinical supervision include parallel processing. If one issue can't be…
Q: Outline the machine language instruction format (i.e., describe how the machine language instruction…
A: Introduction Machine language: The lowest level of programming that a computer can understand is…
Q: Two models, the Rational Unified and the Classical Waterfall, will be compared and contrasted in…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: The Actual Incomplete code in Python- def solve(k,h,knights,hillichurls): # compute and print…
A: In this question we have to write a python code as per the given description. Let's code, hope this…
Q: Identify an organization of your choice that currently operates a manual filing system. Give a…
A: “Since you have posted a question with multiple sub-parts, we will solve the first three sub-parts…
Q: I'd be grateful if you could elaborate on the three rules that should be followed by everyone who…
A: Introduction: Integrity constraints or rules in a database system ensure data integrity. Entity,…
Q: The values have been put into a single pool, and a hash map that was not constructed with much care…
A: Please refer to the following step for the complete solution to the problem above.
Q: To what extent do you have say over how old systems evolve? When will it be more affordable to…
A: Answer: We need to explain the how old systems evolve and when required replacement rather than…
Q: Talk about how the Internet has changed over the years and the many technologies that have made this…
A: Information technology includes databases, communications software, networks, and PDAs. The Internet…
Q: If these three factors are not met, a network's efficacy and efficiency will be compromised. Can you…
A: Introduction Networking is the practice of connecting two or more devices together in order to…
Q: For instance, you may safeguard the network in your house by employing personal firewalls and…
A: Introduction: Computers are protected against hazardous invasions by "firewalls."
Q: Show the C++ code segment that declares an enumeration type called AccessLevel, where the…
A: Here is the C++ code segment that declares the enumeration type AccessLevel and an identifier…
Q: Specify, compare, and contrast several forms of back-end compiler architectures.
A: Introduction: A two-pass/multi-pass compiler is one that processes a program's source code or…
Q: Which three components are necessary for a network to operate efficiently and effectively? Give me…
A: Performance, dependability, and security are crucial to network functioning. Users, transmission…
Q: Try commenting out your thread code and summing all of the integers from 1 to 2000. How long does it…
A: In this question, it is asked to calculate the elapsed time in case the concept of threading is used…
Q: Which of the following C# expressions is equivalent to a b > a B: two of these C: a = b D: ! (b…
A: Introduction : The object-oriented programming language C# is used to create a wide range of…
Q: when do you think it would be best to start using brouter on your network?
A: Introduction : BRouter is an open-source routing engine for Android and Java-enabled devices. It…
IN JAVA
Implement the method
public void display()
which displays the entries in a stack starting from the top. If the stack is empty, print “The stack is empty”.
Add the method to ArrrayStack2.java. You do not need to modify StackInterface.java.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Complete ArrayStack.java, an array-based implementation o the Stack.java interface. Modify only the bodies of the following methods in the ArrayStack class: push pop top isEmpty isFull Nothing else should be modified in ArrayStack. Write the class ArrayStackTest to test your implementation. Print only the names of the tests and error messages. Give the test method meaningful names (e.g., emptyStackTest). Test push, pop, top, and isEmpty immediately after the stack has been instantiated. Push an element on an empty stack. Test pop, top, and isEmpty. Instantiate a stack with initialCapacity of 1. Push two elements. Check capacity. Other tests you deem necessary.public interface StackInterface void push (T element) throws StackoverfloWException; void pop () throws StackUnderflowException; T top () throws StackUnderflowException; boolean isFul1 (); boolean isEmpty(); Show what is written by the following segments of code (see printın on the code), given that iteml, item2, and item3 are int variables, and ali is an object that fits the abstract description of a stack as shown above StackInterface. Assume that you can store and retrieve variables of type int on ali. iteml = 2; item2 = 0; item3 = 6; ali.push (item2); ali.push (item1); ali.push ( iteml+item3); item2 = ali.top ( ); ali.push (item3*item3); ali.push (item2); ali.push (3); iteml = ali.top ( ); ali.pop( ); System.out.println (iteml + " " + item2 + while (!ali.isEmpty( )) + item3); iteml = ali.top( ) ; ali.pop () ; System.out.println (item1) ;In Java Write a method splitStack that takes a stack of integers as a parameter and splits it into negatives and non-negatives. The numbers in the stack should be rearranged so that all the negatives appear on the bottom of the stack and all the non-negatives appear on the top. In other words, if after this method is called you were to pop numbers off the stack, you would first get all the non-negative numbers and then get all the negative numbers. It does not matter what order the numbers appear in as long as all the negatives appear lower in the stack than all the non-negatives. You may use a single queue as temporary storage.
- Implement a simple stack in java using the scenario below. A company wishes to keep track of the order in which it employed staff. Users can enter either "f" to fire, "h" to hire or "e" to end the program. When a member of staff is employed, their employee number is added to the top of a stack when someone has to be made redundant, the last person to join the company is removed from the top of the stack. Hint: Use ArrayListUse stacks from the STL to implement a video game library functionality. In this implementation, consider a VideoGame class with title, release year, genre and publisher as variables. Provide setters and getters to these variables. In main, create a stack of video games. Add 5 different game objects into the stack. Then in a loop, for each item that you retrieve from the stack display the game information as follows: TITLEYEARGENREPUBLISHERAssignment2: Analyse the case study given in chapter 4 stackAnswer the following questions from the Maze.java1. Write the different class names with class keyword2. Write the different methods using public and private keywords3. Write import statements used in maze.java4. Write the main method chapter 4 stack : https://drive.google.com/file/d/1m6UicIA-IR1qde-TY1fhzlwMMxygHhPF/view?usp=sharing
- The implementation of a queue in an array, as given in this chapter, uses the variable count to determine whether the queue is empty or full. You can also use the variable count to return the number of elements in the queue. On the other hand, class linkedQueueType does not use such a variable to keep track of the number of elements in the queue. Redefine the class linkedQueueType by adding the variable count to keep track of the number of elements in the queue. Modify the definitions of the functions addQueue and deleteQueue as necessary. Add the function queueCount to return the number of elements in the queue. Also, write a program to test various operations of the class you defined.Computer Science create a method +addToList(o:E):void that adds the object (o) to the ArrayList referenced by the instance variable list. create a method +removeFromBackOfList():E that removes the object at the back of the ArrayList and returns it.Write a java program called ShoppingList.java, which prompts the user to enter a set of grocery items, and stores them in a list using the Java ArrayList Collection class. It then displays the list and asks the user to type in each item when they put it in their shopping cart and remove it from the list. It should work as follows: Welcome to My Shopping List. Please enter an item: Milk Enter another Item Y/N: Y Please enter an item: Bread Enter another Item Y/N: Y Please enter an item: Eggs Enter another Item Y/N: N Here is your Shopping List: Milk Bread Eggs Enter an item to remove from the list: Eggs Eggs has been removed Here is your Shopping List: Milk Bread Enter an item to remove from the list: Milk Milk has been removed Here is your Shopping List: Bread
- class. The StackUnderflowException class extends the Java Answer:Given a stack of positive integers, write a Java method called movePrimes that rearranges elements of the stack such that all prime numbers are below none primes regardless to the order of primes. Note: You are allowed to create only one other stack. You can not use other data structures such as array, arraylist, queue, ....etc. Consider the following example:Assignment2: Analyse the case study given in chapter 4 stackAnswer the following questions from the Maze.java4. Write the main method chapter 4 stack : https://drive.google.com/file/d/1m6UicIA-IR1qde-TY1fhzlwMMxygHhPF/view?usp=sharing

