Limit: 2 The consecutive sum: 1 + 2 = 3 Limit: 10 The consecutive sum: 1+ 2+ 3+ 4 = 10 Limit: 18 The consecutive sum: 1+ 2+ 3+ 4+ 5+ 6 = 21 Sample output Sample output Sample output
Limit: 2 The consecutive sum: 1 + 2 = 3 Limit: 10 The consecutive sum: 1+ 2+ 3+ 4 = 10 Limit: 18 The consecutive sum: 1+ 2+ 3+ 4+ 5+ 6 = 21 Sample output Sample output Sample output
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 10PE
Related questions
Question
Can you use Python
Thank you very much!

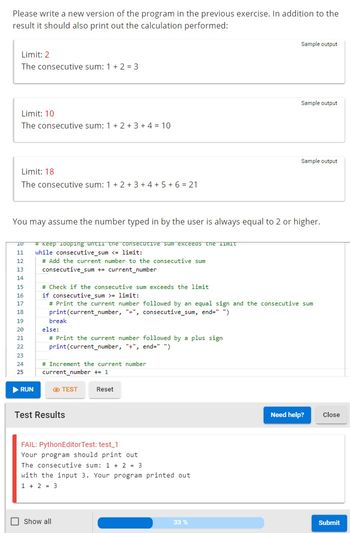
Transcribed Image Text:Please write a new version of the program in the previous exercise. In addition to the
result it should also print out the calculation performed:
Limit: 2
The consecutive sum: 1 + 2 = 3
Limit: 10
The consecutive sum: 1 + 2 + 3 + 4 = 10
Limit: 18
The consecutive sum: 1+ 2+ 3+ 4+ 5+ 6 = 21
Sample output
1 # Write your solution here
Sample output
Sample output
You may assume the number typed in by the user is always equal to 2 or higher.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
Hello,Its not correct...Can you help me?
Transcribed Image Text:Please write a new version of the program in the previous exercise. In addition to the
result it should also print out the calculation performed:
Limit: 2
The consecutive sum: 1 + 2 = 3
Limit: 10
The consecutive sum: 1+ 2+ 3+ 4 = 10
Limit: 18
The consecutive sum: 1+ 2+ 3+ 4+ 5+ 6 = 21
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
You may assume the number typed in by the user is always equal to 2 or higher.
▶ RUN
# Keep looping until the consecutive sum exceeds the limit
while consecutive_sum <= limit:
# Add the current number to the consecutive sum
consecutive_sum += current_number
break
else:
# Print the current number followed by a plus sign
print(current_number, "+", end=" ")
# Check if the consecutive sum exceeds the limit
if consecutive_sum >= limit:
# Print the current number followed by an equal sign and the consecutive sum
print(current_number, "-", consecutive_sum, end=" ")
# Increment the current number
current_number += 1
TEST
Test Results
Reset
FAIL: PythonEditorTest: test_1
Your program should print out
The consecutive sum: 1 + 2 = 3
Show all
with the input 3. Your program printed out
1 + 2 = 3
Sample output
Sample output
33 %
Sample output
Need help? Close
Submit
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning