
Practice Problem 5.6 (solution page 575)
Let us continue exploring ways to evaluate polynomials, as described in Practice Problem 5 5. We can reduce the number of multiplications in evaluating a polynomial by applying Horner’s method, named after British mathematician William G. Horner (1786-1837). The idea is to repeatedly factor out the powers of x to get the following evaluation:
a0+x(a1+x(a2+···x(an-1+xan)···)) (5.3)
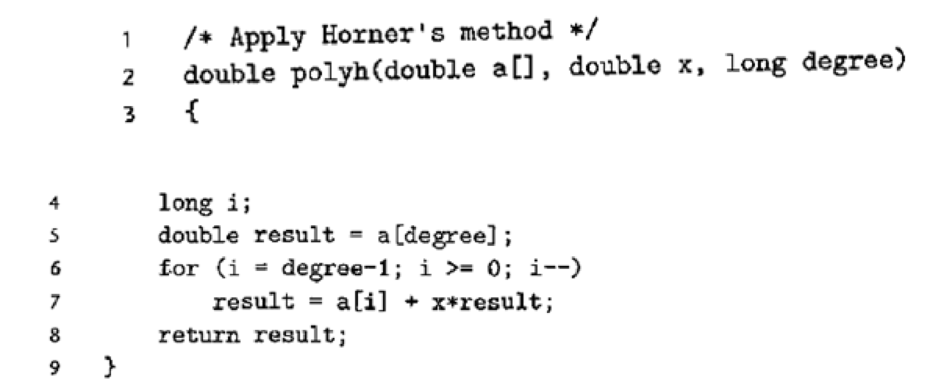
Using Horner's method, we can implement polynomial evaluation using the following code:
- A. For degree n, how many additions and how many multiplications does this code perform?
- B. On our reference machine, with the arithmetic operations having the latencies shown in Figure 5.12, we measure the CPE for this function to be 8.00. Explain how this CPE arises based on the data dependencies formed between iterations due to the operations implementing line 7 of the function.
- C. Explain how the function shown in Practice Problem 5.5 can run faster, even though it requires more operations.
Want to see the full answer?
Check out a sample textbook solution
Chapter 5 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Additional Engineering Textbook Solutions
C Programming Language
Starting Out With Visual Basic (7th Edition)
Starting Out with Java: From Control Structures through Data Structures (4th Edition) (What's New in Computer Science)
Java How To Program (Early Objects)
Objects First with Java: A Practical Introduction Using BlueJ (6th Edition)
C++ How to Program (10th Edition)
- Problem 1 (Ransom Note Problem) in python A kidnapper kidnaps you and writes a ransom note. He does not write it by hand to avoid having his hand writing being recognized, so he uses a magazine to create a ransom note. We need to find out, given the ransom string and magazine string, is it possible to create a given ransom note. The kidnapper can use individual characters of words. Here is how your program should work to simulate the ransom problem: your program should prompt the user to enter a long String to represent the magazine and another short String to represent the required ransom note. your program needs to check if the magazine string contains all required characters in equal or greater number present in the ransom note. your program should print true if it is possible to create the given ransom note from the given magazine, and print false otherwise. Break up your code into a set of well-defined functions. Each function should include a comment block that briefly describes…arrow_forward[Problem 4] Consider the sequence of integers 0, 1, 1, 7, 13, 55, 133, 463.. a) find the recursive function and initial conditions which generates them b) using the solution in part a), find the closed form solution for this sequence c) implement the recursive function in Pythonarrow_forwardRedo problem 2 where you have to define and use the following functions: (a) isTriangle - takes 3 sides of a triangle and returns true if they form a triangle, false otherwise. (b) isIsosceles - takes 3 sides of a triangle and returns true if they form an isosceles triangle, false otherwise. (c) isEquilateral - takes 3 sides of a triangle and returns true if they form anequilateral triangle, false otherwise. (d) isRight - takes 3 sides of a triangle and returns true if they form a right triangle, false otherwise. (e) your program should run continuous until the user wants to quit this is my problem 2: #include <iostream> #include <cmath> using namespace std; // Constant Declarations const double E = .0001; int main() { double side1, side2, side3; bool isTriangle, isRight, isEquilateral, isIsosceles; cout << "Enter the lengths of the 3 sides of a triangle -- "; cin >> side1 >> side2 >> side3; isTriangle = side1 + side2 > side3 &&side1 +…arrow_forward
- 2, Towers of Hanoi Problem. (10 points) The Towers of Hanoi is a famous problem for studying recursion in computer science and searching in artificial intelligence. We start with N discs of varying sizes on a peg (stacked in order according to size), and two empty pegs. We are allowed to move a disc from one peg to another, but we are never allowed to move a larger disc on top of a smaller disc. The goal is to move all the discs to the rightmost peg (see figure). To solve the problem by using search methods, we need first formulate the problem. Supposing there are K pegs and N disk. Answer the following questions. (1) Determine a state representation for this problem. (4points) (2) What is the size of the state space? (3 points) (3) Supposing K=3, N=4, what is the start state by using your proposed state representation method and what is the goal state? (3 points)arrow_forwardQ27) An approximation for the exponential function can be found using what is called a Maclaurin series: x' x? x3 et x 1+ 1! + +... 2! 3! Write a program to investigate the value of e and the exp function.arrow_forward3. [10 points.] Show that these three statements are equivalent, where a and b are real numbers: (i) a is less than b, (ii) the average of a and b is greater than a (iii) the average of a and b is less than b.arrow_forward
- 2. (13-09-2022) Let n number of identical small boxes are there where each of the first i boxes contains a diamond and remaining ni are empty. Harry Potter got two magic sticks that can test whether a box is empty or not in a single touch, except that a magic stick vanishes if he tests it on an empty box. How Harry Potter knows the value of i using two magic sticks to determine all the boxes containing pearls using at most o(n) touches?arrow_forwardComputer Science c++ || urgent Write the code for choosing the list of items in order to get the maximum profit of fractional knapsack problem. [NOTE: number of input items should be user interest, and output should be like - firstly print the resulting profit table, and then print the all selected items (must not be all items from the inputted items - means that all inputted items should not be as the selected items) for the knapsack and then print the maximum profit.]arrow_forwardHW11_2 (textbook 21.14) A plane is being tracked by radar, and data are taken every second in polar coordinates 0 and r t (s) 200 202 204 206 208 210 e (rad) 0.75 0.72 0.70 0.68 0.67 0.66 r (m) 5120 5370 5560 5800 6030 6240 At 206 seconds, use the centered finite-difference (second order correct) to find the vector expressions for velocity i and å. The velocity and acceleration given in polar coordinates are v = rë, + rôë, and a = (* – rô?)ẽ, +(rö + 2rô)ẽg Write a MATLAB script to implement the above | use fprintf to display the magnitudes of velocity and acceleration at 206 seconds.arrow_forward
- PROBLEM 17. [TIME ALLOWED = 5 MINUTES] State whether “n is divisible by 9” is (a) necessary, (b) sufficient, or (c) neither necessary nor sufficient for “n is divisible by 6”, where n is a natural number.arrow_forwardA) Shanon Code B) Shanon-Fano Code for the following Set of massages: [P(X)] =x*.s*04 02 021 X 2 хз х 4 X5 0.05 0.15 0.4 0.2 0.2 Find the code efficiency ?arrow_forward2. RADIOACTIVE DECAY, REVISITED This is a modified version of chapter 1 problem 4 in your textbook. Consider the radioactive decay of nuclei A into nuclei B, which can then also decay. The numbers of each species as a function of time are given by N₁ (t) and NB (t), and the decay of each species is governed by¹: dNA dt == NA dNB NA NB = dt ΤΑ TB where T and T are the decay time constants for each type of nucleus.arrow_forward
 C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr
